In legal investigations, journalism, and corporate security, audio recordings often serve as key pieces of evidence. But what happens when the authenticity of that audio is in question? This is where audio tampering detection comes into play—a critical component of forensic analysis that ensures integrity and truth in high-stakes scenarios. In this blog, we’ll explore how audio forensic experts identify tampering, the common red flags they look for, and how this work intersects with mobile device forensics and digital video forensics.

Understanding Audio Tampering
Audio tampering refers to any unauthorized or deceptive modification of an audio recording. This can include deletions, insertions, splices, or manipulation of speech patterns to distort meaning. Tampering may be done to mislead listeners, alter evidence, or present a false narrative.
The ability to detect these alterations is crucial. False evidence can mislead courts, sabotage careers, or threaten public safety. Hence, audio tampering detection is an indispensable skill in forensic science, requiring a blend of technology, experience, and investigative techniques.
The Role of an Audio Forensic Expert
An audio forensic expert is trained to analyze sound recordings for signs of manipulation. Their job involves verifying authenticity, identifying edits, and presenting their findings in court if necessary. These experts use specialized tools and methodologies to examine recordings across multiple dimensions—such as waveform analysis, metadata inspection, and acoustic consistency.
Their analysis is often part of a broader forensic investigation that may include mobile device forensics and digital video forensics, providing a complete picture of events.
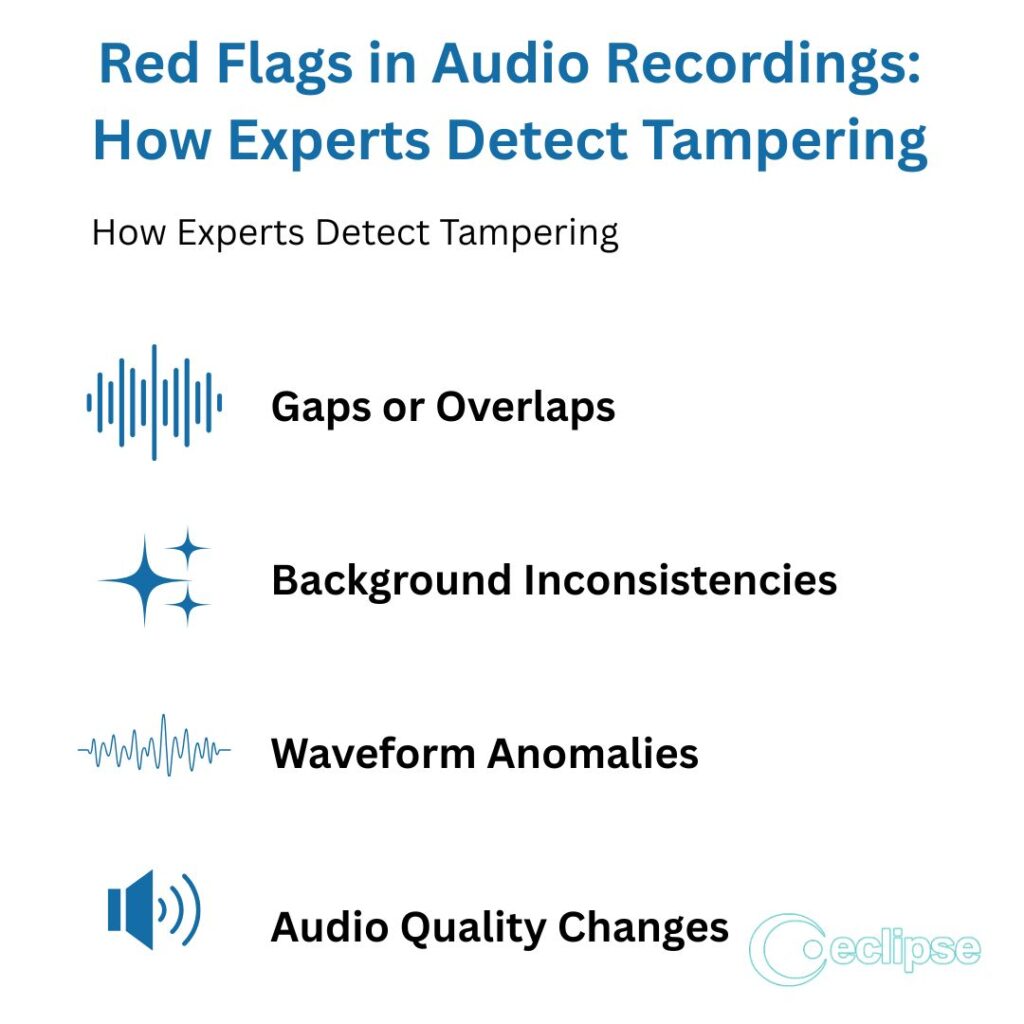
Red Flags Experts Look For in Audio Recordings
1. Inconsistent Background Noise
One of the most obvious signs of tampering is irregular or inconsistent background noise. Real-world environments have a continuous audio signature—ambient sounds like air conditioners, traffic, or room acoustics. A sudden change in these sounds might indicate that portions of the audio were inserted or deleted.
For example, if a speaker’s voice maintains the same volume and tone but the background ambiance shifts, it may suggest the clip has been spliced together from different recordings.
2. Unnatural Pauses or Speech Patterns
Human speech is fluid and generally consistent. If a recording features unnatural gaps, abrupt stops, or strange inflections, it may suggest that the audio has been edited. Audio forensic experts analyze speech rhythm, cadence, and pitch to detect anomalies that may not be perceptible to the average listener.
This includes checking for duplicated phrases or oddly timed silences that could signal content removal.
3. Spectral Discontinuities
Using spectrogram analysis, forensic analysts can visually inspect the frequency content of an audio file. Tampered sections often have frequency patterns that don’t align with the surrounding audio. These spectral discontinuities are difficult to hide and can reveal subtle edits, like overlapping cuts or inserted phrases.
Spectrograms provide a kind of “fingerprint” for the recording, and any break in the continuity is a strong red flag.
4. Metadata Irregularities
Every digital recording carries metadata—details like creation date, file type, recording device, and editing history. If a file’s metadata shows that it was modified after its alleged recording date or edited using software, that’s a critical clue for audio tampering detection.
Although metadata can be altered, a mismatch between the file’s declared history and forensic findings can prompt deeper investigation.

5. Digital Compression Artifacts
When audio is compressed, it often introduces artifacts—imperfections due to reduced data. If different sections of the same recording have varying compression artifacts, it may indicate they originated from separate sources and were stitched together. Audio forensic experts can analyze these discrepancies to reveal tampering.
Tools and Techniques in Audio Tampering Detection
1. Waveform Analysis
This method involves visually examining the audio’s waveform to detect irregularities in amplitude or timing. Sudden spikes, drops, or unnatural silences may indicate cuts or edits. Analysts look for discontinuities that stand out from the overall pattern of the audio.
2. Spectrogram Analysis
Spectrograms help visualize the frequency spectrum over time. Unlike waveforms that show volume, spectrograms display pitch, intensity, and sound texture. Inconsistencies here can signal splicing or signal insertion.
3. Electrical Network Frequency (ENF) Matching
ENF analysis is a powerful forensic tool that uses the background electrical hum recorded from power lines. Since this frequency fluctuates predictably, it can be matched with historical records to verify the time and authenticity of a recording.
4. Acoustic Environment Analysis
This involves evaluating the recording’s environmental acoustics, such as echo patterns or reverberation. If parts of a conversation allegedly occurred in the same location but show different acoustic properties, that’s a serious red flag.
Audio Tampering on Mobile Devices
With the widespread use of smartphones, many recordings under investigation originate from mobile devices. This introduces new challenges—and opportunities—in mobile device forensics. Experts not only analyze the audio file itself but also extract data from the device to verify:
- When and where the recording was made (using GPS stamps)
- Whether audio editing apps were used
- If original files were replaced or renamed

For instance, mobile device forensics might uncover hidden cache files or cloud backups that contain unedited versions of the audio in question, helping to identify tampering.
Correlation with Digital Video Forensics
Tampered audio is often part of altered video content. In digital video forensics, analysts look at both the video and its accompanying audio to detect inconsistencies. Mismatched lip-syncing, inconsistent lighting, or background noise that doesn’t match the video can point to deeper manipulation.
For example, if a security footage clip has audio that doesn’t align with the visual actions—like gunshots occurring without visible flash or speech happening when lips are still—it raises suspicion. Cross-referencing findings from both audio tampering detection and digital video forensics offers stronger evidence of tampering.
The Legal Importance of Audio Integrity
Tampered recordings can destroy reputations or falsely incriminate individuals. This is why audio forensic experts often serve as expert witnesses in court, presenting scientific evidence about the authenticity—or lack thereof—of a recording.
In legal contexts, even the suspicion of tampering can weaken the credibility of evidence. Hence, thorough analysis and clear documentation are essential. A properly conducted forensic investigation can either validate the evidence or expose deceptive practices.
Real-World Cases of Audio Tampering
Case 1: Political Scandal
In a high-profile political investigation, an audio clip was released suggesting a government official’s involvement in corruption. Upon closer examination, audio forensic experts discovered spectral inconsistencies and abrupt changes in background noise. ENF analysis further confirmed that segments were recorded at different times. The expert testimony helped discredit the tape as manipulated.

Case 2: Workplace Harassment Claim
An employee submitted a voice recording to support a harassment claim. However, the company’s legal team requested an independent review. Using audio tampering detection, the forensic analyst found duplicate phrases and irregular acoustic signatures. This supported the employer’s assertion that the recording had been altered.
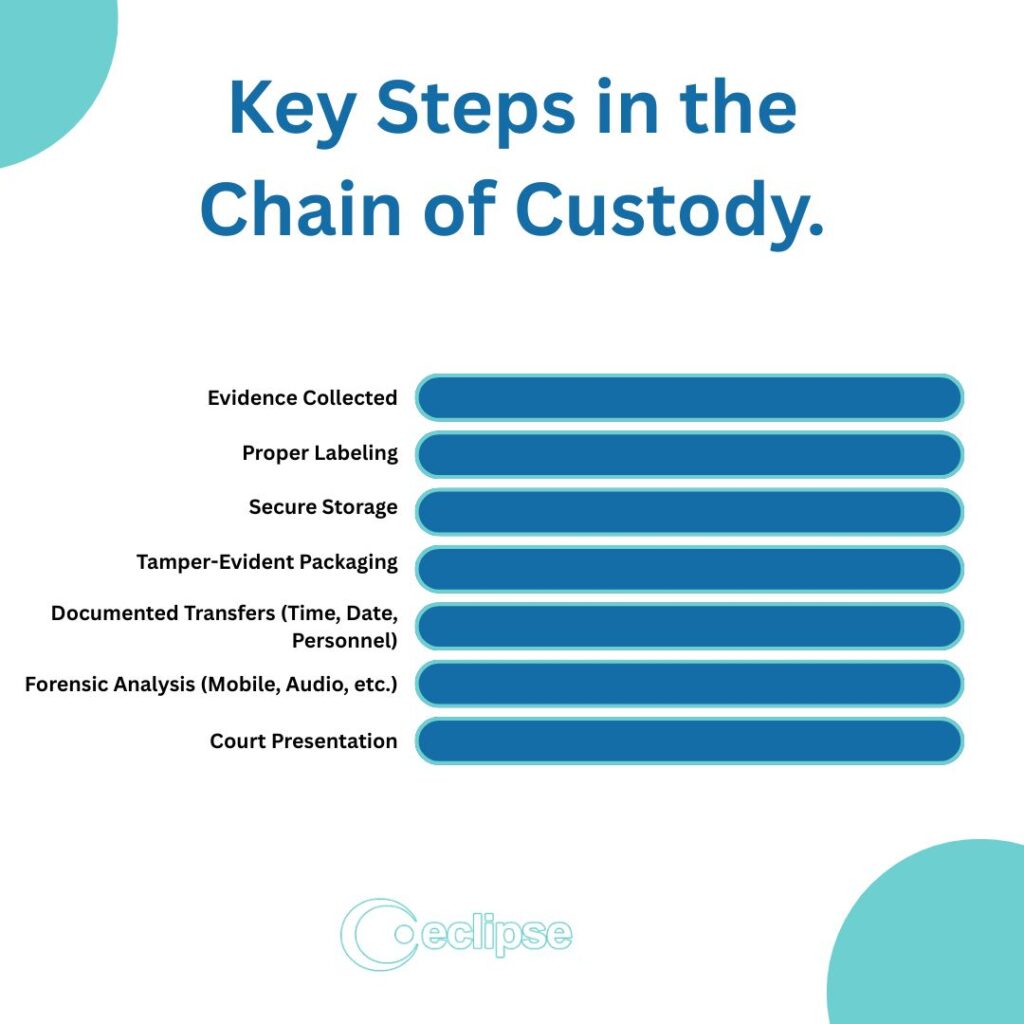
Best Practices to Preserve Audio Integrity
To ensure recordings remain admissible and reliable, it’s crucial to follow best practices:
- Always retain the original file.
- Avoid converting formats unless necessary.
- Document the chain of custody.
- Use secure, time-stamped platforms to store audio.
- Avoid editing or compressing the file after capture.
Following these practices minimizes the risk of accusations of tampering and maintains the integrity of the evidence.
The Value of Forensic Vigilance
As technology advances, so do methods of deception. Detecting audio tampering is no longer a matter of intuition—it’s a science that relies on data, tools, and expertise. Whether investigating criminal behavior, validating journalistic evidence, or resolving corporate disputes, the role of an audio forensic expert is more vital than ever.
With integration from mobile device forensics and digital video forensics, today’s forensic professionals have a robust toolkit for ensuring the truth is heard—literally. In a world where manipulated media can shape opinions and outcomes, forensic vigilance serves as the final barrier against misinformation.
At Eclipse Forensics, we specialize in uncovering the truth behind audio, mobile, and video data. Whether you’re dealing with legal disputes, investigative journalism, or corporate concerns, our team of audio forensic experts provides precise audio tampering detection using cutting-edge technology. We analyze waveforms, spectrograms, and metadata to verify authenticity and expose hidden edits. Leveraging the latest in digital forensics, including mobile device forensics and digital video forensics, we ensure your evidence stands strong. Trust Eclipse Forensics to deliver clear, courtroom-ready reports backed by science. When accuracy matters most, count on our expertise to reveal what really happened, sound by sound, frame by frame. Contact us today for a confidential consultation.