Nowadays, digital data reigns supreme, which is why there is a need to safeguard digital integrity and combat the different types of cybercrime as a priority. Enter cyber forensic experts—skilled professionals adept at navigating the intricacies of digital evidence and investigation.
Let’s explore the importance and benefits of cyber and data forensic experts in preserving evidence and combating cyber threats.
Understanding Cyber Forensics
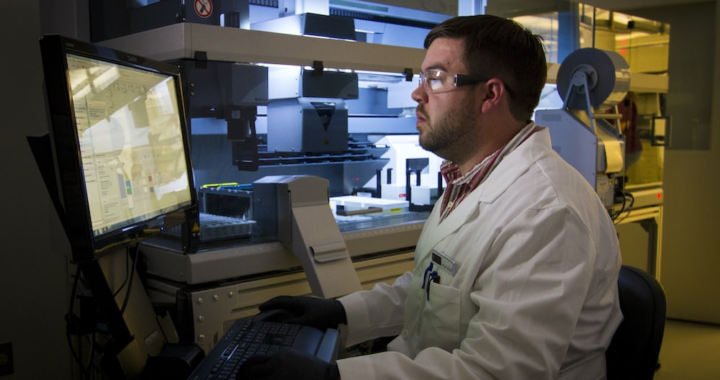
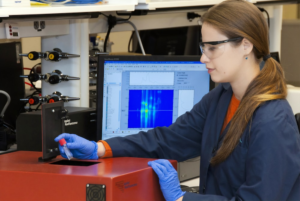
Cyber forensics is the application of investigative techniques to gather and analyze digital evidence in a manner that is admissible in a court of law. It involves extracting, preserving, and interpreting data from various digital sources such as computers, mobile devices, and networks.
Cyber forensic experts possess a deep understanding of digital systems, forensic tools, and investigative methodologies.
The Role of a Cyber Forensic Expert
1. Safeguarding Digital Integrity
One of the primary roles of a cyber forensic expert is to safeguard digital integrity. They assess the security posture of digital systems, identify vulnerabilities, and recommend measures to mitigate risks. Conducting proactive investigations and audits allows them to help organizations fortify their defenses against cyber threats, thereby preventing potential breaches and data compromises.
2. Preserving Evidence
In the event of a cyber incident or crime, preserving evidence is paramount for successful investigation and prosecution. Cyber forensic experts employ specialized tools and techniques to collect and preserve digital evidence in a forensically sound manner.
Whether it’s analyzing hard drives, examining network logs, or retrieving deleted files, their expertise ensures that critical evidence remains intact and admissible in legal proceedings.
3. Investigating Cyber Incidents
When a cyber incident occurs, such as a data breach or a malware attack, cyber forensic experts play a pivotal role in investigating the incident. They analyze the nature and scope of the breach, identify the entry points and vectors of attack, and trace the activities of malicious actors.
Through meticulous examination of digital artifacts and log files, they reconstruct the timeline of events and uncover the root cause of the incident.
4. Combating Cybercrime
Cybercrime is a pervasive threat that spans across industries and sectors. From financial fraud to intellectual property theft, cybercriminals exploit vulnerabilities in digital systems for illicit gains.
Cyber forensic experts are at the forefront of combating cybercrime by gathering actionable intelligence, assisting law enforcement agencies in apprehending suspects, and providing expert testimony in court. Their contributions are instrumental in holding cybercriminals accountable and deterring future cyber-attacks.
5. Ensuring Legal Compliance
In addition to their investigative prowess, cyber forensic experts ensure their activities adhere to legal and regulatory standards. They maintain a chain of custody for digital evidence, document their findings meticulously, and follow established protocols to ensure the integrity and authenticity of evidence.
Upholding the principles of due process and privacy rights helps them contribute to the fair and transparent administration of justice in the digital age.
6. Providing Expert Testimony
In legal proceedings related to cyber incidents, cyber forensic experts often serve as expert witnesses. They provide testimony based on their analysis and findings, helping to elucidate complex technical concepts for judges and juries.
Their expert testimony lends credibility to the evidence presented and can significantly influence the outcome of a case. Cyber forensic experts play a crucial role in serving justice by effectively communicating their findings in court.
7. Enhancing Incident Response Capabilities
Cyber forensic experts are integral members of incident response teams tasked with mitigating the impact of cyber incidents and restoring normal operations. Their swift and systematic approach to analyzing digital evidence helps organizations contain breaches, identify compromised systems, and remediate vulnerabilities.
Collaborating with IT security professionals and other stakeholders allows them to facilitate a coordinated response to cyber threats, minimizing downtime and reputational damage.

8. Supporting Regulatory Compliance
In an increasingly regulated marketplace, compliance with cybersecurity standards and regulations is paramount for organizations across industries. Cyber forensic experts assist organizations in interpreting and implementing regulatory requirements.
They conduct forensic audits, assess data handling practices, and configure systems to meet compliance standards. Aligning cybersecurity practices with regulatory mandates allows cyber forensic experts to help organizations avoid fines, penalties, and legal liabilities.
9. Conducting Digital Fraud Investigations
Digital fraud poses significant risks to individuals, businesses, and governments alike. Cyber forensic experts specialize in investigating various forms of digital fraud, including identity theft, phishing scams, and financial fraud.
Through a thorough examination of digital evidence trails, they uncover the tactics and techniques used by fraudsters, helping victims recover stolen assets and pursue legal action. Their expertise in identifying fraudulent activities is indispensable in mitigating financial losses and restoring trust in digital transactions.
10. Collaborating with Law Enforcement Agencies
Cyber forensic experts collaborate closely with law enforcement agencies to combat cybercrime on a global scale. They provide technical assistance, forensic analysis, and intelligence support to law enforcement investigations into cyber threats and attacks.
Cyber forensic experts help law enforcement agencies identify cybercriminal networks, dismantle illicit operations, and apprehend perpetrators by sharing their expertise and resources. Their collaborative efforts contribute to a safer digital environment for individuals, businesses, and governments worldwide.
11. Advancing Research and Innovation
Cyber forensic experts are at the forefront of advancing research and innovation in digital forensics. They conduct research studies, develop new forensic tools and techniques, and contribute to the evolution of best practices.
Through collaboration with academia, industry partners, and government agencies, they drive advancements in cybersecurity technologies and methodologies. Staying abreast of emerging trends and threats allows cyber forensic experts to empower organizations to adapt and respond effectively to evolving cyber risks.

12. Educating and Training Professionals
Cyber forensic experts play a vital role in educating and training the next generation of cybersecurity professionals. They develop and deliver specialized training programs, workshops, and certifications to equip individuals with the skills and knowledge needed to excel in digital forensics.
They inspire a new generation of cyber defenders and foster a culture of continuous learning and improvement in the cybersecurity community by sharing their expertise and real-world experiences.
13. Conducting Digital Evidence Analysis
Digital evidence analysis is a core competency of cyber forensic experts. They employ a variety of forensic techniques and tools to analyze digital artifacts such as files, emails, and metadata.
Through meticulous examination and interpretation of digital evidence, they uncover crucial insights that support investigative efforts and legal proceedings. Whether it’s identifying suspect behavior or validating alibis, their expertise in digital evidence analysis helps uncover the truth and deliver justice.
14. Mitigating Insider Threats
Insider threats pose a significant risk to organizations, as trusted insiders with access to sensitive information may intentionally or inadvertently compromise security. Cyber forensic experts specialize in detecting, investigating, and mitigating insider threats by monitoring user activities, analyzing access logs, and conducting forensic examinations.
Through proactive monitoring and threat detection, they help organizations identify potential insider threats and implement controls to prevent data breaches and unauthorized disclosures.
15. Supporting Incident Recovery and Business Continuity
Following a cyber incident, cyber forensic experts play a crucial role in supporting incident recovery and ensuring business continuity. They assist organizations in assessing the extent of the damage, restoring compromised systems, and implementing measures to prevent future incidents.
Working closely with IT teams and management allows them to help expedite the recovery process, minimize disruption to operations, and safeguard the organization’s reputation and bottom line.

The Bottom Line
In an increasingly interconnected world, the role of cyber forensic experts is significant. From safeguarding digital integrity to combating cybercrime, their expertise is indispensable in preserving the trust and security of digital systems.
As organizations continue to navigate the complex landscape of cybersecurity threats, investing in cyber forensic capabilities is not just prudent—it’s essential for staying ahead of emerging threats and protecting against potential liabilities.
Unlock the Power of Cyber Forensics with Eclipse Forensics
Ready to fortify your digital defenses and safeguard your organization against cyber threats? Partner with Eclipse Forensics today and harness the expertise of our data forensic experts. From proactive security assessments to incident response and litigation support, we offer comprehensive digital forensic services tailored to your needs.
Don’t wait until it’s too late—take proactive steps to protect your digital assets and preserve the integrity of your organization.
Contact our digital forensic consultants now to learn more about how Eclipse Forensics can empower your cybersecurity strategy.