In today’s digital landscape, the reliance on technology is ever-increasing. As a result, the need for specialized services in computer forensics has become paramount. Computer forensics involves the collection, preservation, analysis, and presentation of electronic data in a manner that is legally admissible. This blog will explore the integration of computer forensics across various industries, highlighting key players such as video enhancement experts, digital forensic services, and forensic audio specialists.
Understanding Computer Forensics
Computer forensics is a branch of forensic science that deals with the investigation of computers and digital devices. It is primarily used in legal matters, where the integrity of digital evidence can significantly impact the outcome of a case. Computer forensic experts employ various techniques and tools to extract data from devices while maintaining a clear chain of custody. Their findings can be crucial in criminal investigations, civil litigation, corporate disputes, and more.
Key Components of Computer Forensics
- Data Collection: The first step involves gathering relevant data from digital devices. This can include hard drives, mobile phones, servers, and cloud storage.
- Data Preservation: Ensuring that the data remains unaltered is critical. Experts create forensic images or clones of the original data to analyze without risking contamination.
- Data Analysis: Forensic professionals examine the collected data for evidence. This process involves recovering deleted files, analyzing user activity, and identifying anomalies.
- Reporting and Presentation: The final step involves compiling the findings into a clear report that can be presented in a court of law or used in internal investigations.
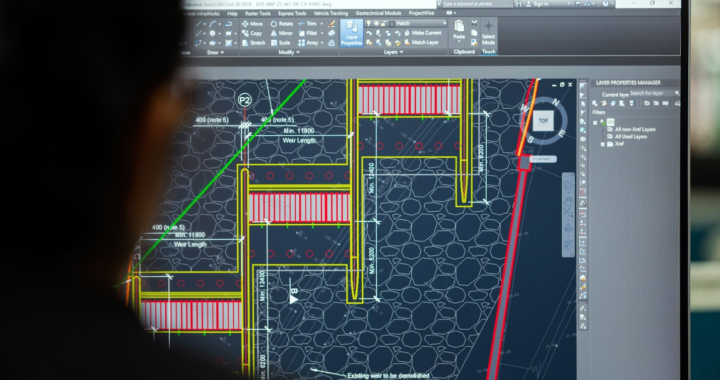
1. Video Enhancement Expert: Enhancing Visual Evidence
In fields such as law enforcement, entertainment, and security, video footage plays a crucial role in evidence collection and analysis. However, the quality of this footage can vary significantly, making it challenging to extract valuable information. This is where a video enhancement expert comes into play.

The Role of Video Enhancement Experts
Video enhancement experts specialize in improving the quality of video footage to make it clearer and more usable for investigations. Their skills are essential in:
- Law Enforcement: Enhancing surveillance footage from crime scenes can provide critical evidence. This can involve sharpening images, increasing resolution, and stabilizing shaky videos to identify suspects or vehicles.
- Legal Proceedings: In court cases, high-quality video evidence can sway juries. Video enhancement experts ensure that the footage presented is as clear and reliable as possible, thus supporting the integrity of the evidence.
- Insurance Claims: In cases of accidents, enhanced video footage can clarify events, assisting insurance companies in making informed decisions about claims.
Techniques Used by Video Enhancement Experts
- Super Resolution: This technique combines multiple frames of low-resolution video to create a higher resolution image.
- Noise Reduction: Reducing visual noise can help in clarifying details in the footage.
- Frame Interpolation: This technique creates intermediate frames between existing frames, resulting in smoother playback and clearer motion.
- Color Correction: Adjusting the color balance can enhance the visibility of crucial details that may otherwise go unnoticed.
2. Digital Forensic Services: A Comprehensive Approach
Digital forensic services encompass a wide range of activities beyond just computer forensics. They are integral to various sectors, including finance, healthcare, and corporate environments.

Importance of Digital Forensic Services
- Cybersecurity: With the rise in cybercrime, digital forensic services are essential for investigating breaches and analyzing threats. These services help organizations understand how an attack occurred and how to prevent future incidents.
- Corporate Investigations: Companies may engage digital forensic services to investigate internal issues such as fraud, intellectual property theft, or employee misconduct. This can involve analyzing emails, documents, and other digital communications.
- Regulatory Compliance: Many industries are subject to regulations regarding data protection and privacy. Digital forensic services help ensure compliance by investigating potential breaches and ensuring proper data handling practices.
- Incident Response: When a cyber incident occurs, rapid response is crucial. Digital forensic experts assist organizations in identifying vulnerabilities, securing systems, and gathering evidence for potential legal action.
Techniques Employed in Digital Forensic Services
- Network Forensics: Analyzing network traffic to identify suspicious activity and trace the origin of cyber threats.
- Mobile Device Forensics: Extracting data from mobile devices, including call logs, messages, and app data, which can be crucial in investigations.
- Cloud Forensics: Investigating data stored in cloud environments, which presents unique challenges in terms of data access and ownership.

3. Forensic Audio Specialists: Clarifying the Soundscape
In addition to visual evidence, audio recordings can be pivotal in investigations. Forensic audio specialists focus on the analysis of audio recordings, enhancing clarity, and determining the authenticity of recordings.
The Role of Forensic Audio Specialists
Forensic audio specialists play a vital role in various sectors, including law enforcement, media, and legal services. Their expertise can be utilized in:
- Criminal Investigations: Analyzing audio recordings from 911 calls, witness statements, or surveillance audio can provide insights into criminal activities.
- Legal Proceedings: Audio evidence can be instrumental in court cases. Forensic audio specialists ensure that recordings are clear and accurate, which can impact the case’s outcome.
- Public Relations: In high-profile cases, audio leaks can damage reputations. Specialists can authenticate recordings and determine if they have been tampered with.
Techniques Used by Forensic Audio Specialists
- Noise Reduction: This technique involves eliminating background noise to enhance the clarity of the main audio.
- Spectral Analysis: Analyzing the frequency spectrum of an audio filecan reveal hidden sounds or anomalies, aiding in the identification of specific voices or noises.
- Time Stretching and Pitch Shifting: Adjusting the speed and pitch of audio can help in clarifying spoken words, making them easier to understand.
- Authentication and Validation: Forensic audio specialists employ techniques to determine whether audio files have been altered, ensuring the integrity of the evidence.
4. The Intersection of Computer Forensics and Other Industries
Computer forensics is not confined to law enforcement or legal environments; it intersects with various industries, demonstrating its versatility and importance.
Financial Sector
In the financial industry, the integrity of digital transactions is paramount. Computer forensics helps in:
- Fraud Detection: Forensic experts analyze digital records to identify discrepancies that may indicate fraudulent activities.
- Data Breach Investigations: When breaches occur, forensic teams are deployed to assess the damage and recover stolen data.

Healthcare Industry
In healthcare, protecting patient data is critical. Computer forensics plays a role in:
- Data Integrity: Ensuring that patient records remain secure and unaltered, thus maintaining trust in healthcare systems.
- Incident Response: In the event of a data breach, forensic teams work to identify vulnerabilities and protect sensitive information.
Education Sector
Educational institutions increasingly rely on digital technology for teaching and administration. Computer forensics assists in:
- Academic Integrity: Investigating cases of plagiarism or cheating through digital means.
- Data Protection: Ensuring that student records and personal information are safeguarded against unauthorized access.
Telecommunications
In telecommunications, where data transfer is critical, computer forensics helps in:
- Data Recovery: Retrieving lost or deleted data from devices, ensuring that communication records are preserved.
- Cybersecurity: Analyzing breaches in telecommunications infrastructure and securing communication channels.
5. Challenges and Future Trends in Computer Forensics
While computer forensics has made significant strides, it faces various challenges that professionals must navigate.
Challenges
- Rapid Technological Advancements: As technology evolves, so do the methods used by cybercriminals Forensic experts must continuously update their skills and tools to keep pace.
- Data Volume: The sheer volume of data generated daily presents a challenge in terms of storage and analysis.
- Encryption and Privacy: As encryption becomes more widespread, accessing data can be challenging for forensic experts.
- Legal Implications: The legal landscape surrounding digital evidence is still evolving, requiring experts to stay informed about regulations and best practices.

Future Trends
- Artificial Intelligence and Machine Learning: These technologies are being integrated into forensic tools to enhance data analysis and anomaly detection.
- Cloud Forensics: As more businesses move to the cloud, specialized techniques will emerge to investigate cloud-based data.
- Mobile Device Forensics: The increasing use of mobile devices necessitates advanced tools for extracting and analyzing data from these platforms.
- Cybersecurity Integration: Collaboration between cybersecurity professionals and forensic experts will become more prevalent, leading to a more comprehensive approach to digital threats.
At Eclipse Forensics, we understand the critical importance of reliable digital evidence in today’s technology-driven world. Our team of experts, including video enhancement expoerts and forensic audio specialists, provides comprehensive digital forensic services tailored to your needs. Whether you’re facing a complex legal case or need support with corporate investigations, our dedicated professionals are here to help.
Don’t leave your digital evidence to chance—trust Eclipse Forensics to deliver the clarity and accuracy you require. Contact us today to learn more about our services and how we can assist you with your forensic needs.