Courtrooms demand clarity. Judges and juries expect answers, not algorithms. They want facts, not technical jargon. That expectation places enormous responsibility on forensic professionals who deliver expert witness testimony.
Technical evidence often involves complex systems, hidden data structures, metadata timelines, and forensic extraction tools. Without a clear explanation, even the strongest findings lose impact. Skilled experts translate complexity into clarity. They convert digital traces into understandable narratives. They connect evidence to real-world meaning.
This guide explains how forensic professionals present technical findings clearly, confidently, and credibly in court.
Why Clarity Determines Credibility
Jurors rarely hold technical backgrounds. Many struggle with terms like hash values, packet logs, or deleted file recovery. When an expert overloads the courtroom with technical language, confusion replaces confidence.
Strong expert testimony achieves three critical goals:
- It explains findings in plain language.
- It demonstrates reliable methodology.
- It builds trust through transparency.
Clarity strengthens credibility. When jurors understand how the expert reached conclusions, they feel confident relying on those conclusions.
Start With the Narrative, Not the Data
Forensic experts must frame evidence within a logical story. Data alone rarely persuades. Context persuades.
Before presenting technical details, an expert should answer three foundational questions:
- What issue required investigation?
- What process uncovered the evidence?
- What conclusions emerged from that process?
A computer forensics expert witness should avoid diving straight into technical extraction procedures. Instead, they should outline the investigation’s objective. For example:
- “I examined the laptop to determine whether deleted emails existed.”
- “I analyzed the mobile device to identify message activity on a specific date.”
This approach orients the courtroom. It gives jurors a mental roadmap before technical explanations begin.

Translate Technical Language Into Everyday Terms
Technical evidence often includes complex terminology. Experts must convert specialized language into accessible concepts.
Instead of saying:
- “I extracted volatile memory artifacts.”
Say:
- “I recovered temporary system data that the device stored while it operated.”
Instead of:
- “The metadata revealed timestamp anomalies.”
Say:
- “The file’s internal record showed a date that did not match the claimed creation time.”
Every explanation should reduce friction. Jurors should never struggle to decode meaning.
Clear expert witness testimony relies on analogies when appropriate. For example:
- Compare metadata to a digital fingerprint.
- Compare deleted file recovery to retrieving shredded documents from a secure bin.
These comparisons create mental anchors. They help jurors visualize invisible processes.
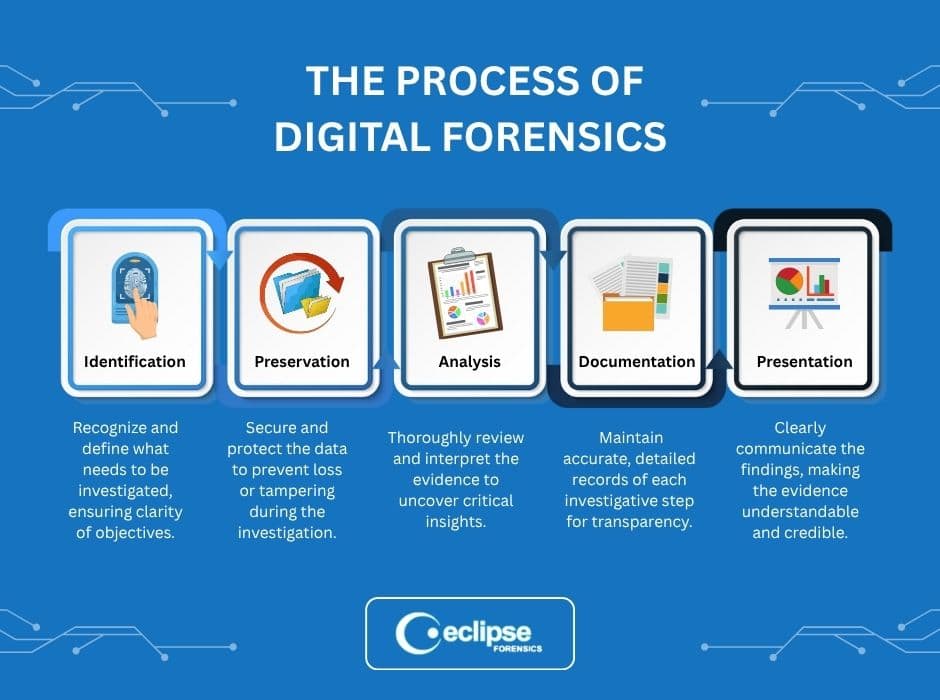
Demonstrate Methodology Step by Step
Jurors trust process. They need to understand not just what you found, but how you found it.
When presenting findings, a forensic professional should:
- Describe evidence collection procedures.
- Explain preservation techniques.
- Outline analysis tools.
- Clarify validation methods.
- Present conclusions.
This structured presentation strengthens the integrity of court certified forensics work. It shows adherence to recognized standards. It reinforces that the expert followed repeatable procedures rather than guesswork.
A methodical explanation also prepares the expert for cross-examination. When opposing counsel challenges findings, the expert can confidently walk back through each step.

Use Visual Aids Strategically
- Digital evidence often benefits from visual reinforcement.
- Timelines clarify sequences.
- Side-by-side comparisons expose alterations.
- Callouts highlight critical metadata.
However, visuals must simplify rather than complicate. Overloaded slides weaken impact. Each graphic should serve a single purpose.
A computer forensics expert witness should guide jurors through visuals deliberately:
- Point to the key timestamp.
- Highlight the relevant message thread.
- Explain each image before moving forward.
Clear visuals combined with direct explanation elevate expert testimony from technical to persuasive.
Maintain Composure Under Cross-Examination
Opposing counsel often attempts to undermine credibility. They may challenge tools, question procedures, or imply bias.
A strong expert responds with calm precision. They avoid defensiveness. They answer directly. They remain grounded in facts.
Confidence grows from preparation. Experts should:
- Review case notes thoroughly.
- Revisit analytical procedures.
- Anticipate common challenges.
- Practice concise responses.
When a forensic professional delivers steady expert witness testimony, jurors notice. Composure communicates authority.
Avoid Overstatement
Experts must remain objective. Overreaching damages credibility instantly.
Instead of claiming:
- “This proves the defendant altered the file.”
Say:
- “The forensic analysis shows the file’s timestamp changed after its original creation date.”
Stick to facts. Let attorneys argue implications. The expert’s role involves explaining evidence, not advocating conclusions. Objective expert testimony carries more weight than dramatic claims.
Establish Qualifications Without Arrogance
Jurors need to trust the expert’s background. Credentials matter. Experience matters. Certifications matter.
However, experts should present qualifications with clarity, not ego.
A brief explanation should include:
- Years of forensic experience.
- Specialized certifications.
- Relevant case history.
- Technical training.
Professionals working in court certified forensics must emphasize adherence to recognized standards. This reinforces legitimacy without sounding promotional. Jurors respond well to expertise delivered with humility.
Prepare for Simplification Without Distortion
Simplifying technical findings does not mean diluting accuracy. Experts must preserve precision while removing unnecessary complexity. This balance defines effective expert witness testimony.
For example:
Instead of reciting a full forensic hash verification process, an expert can explain:
- “I used a digital verification method that ensures the data remained unchanged from the time of collection.”
That statement communicates integrity without overwhelming detail. If opposing counsel requests deeper explanation, the expert can expand.
Address Weaknesses Proactively
Every investigation includes limitations. Devices may contain partial data. Logs may show gaps. Certain timestamps may lack context.
Strong experts acknowledge limitations openly. Transparency builds credibility.
A computer forensics expert witness might state:
- “The device did not retain location data beyond 30 days.”
- “The application overwrote earlier messages automatically.”
This approach prevents opposing counsel from weaponizing those gaps. It shows honesty. Jurors respect candor.
Structure Testimony for Maximum Impact
Effective expert testimony follows a logical arc:
- Qualifications
- Assignment scope
- Evidence collection
- Analytical methods
- Findings
- Conclusions
This progression mirrors how people process information. It builds understanding gradually. It avoids cognitive overload.
Each section should transition naturally. Avoid abrupt shifts between topics. Flow strengthens comprehension.

Emphasize Integrity at Every Stage
Digital evidence requires careful handling. Chain of custody, forensic imaging, validation procedures, and secure storage all protect integrity.
Professionals practicing court certified forensics must communicate those safeguards clearly. They should explain:
- How they preserved original data.
- How they verified authenticity.
- How they prevented contamination.
Jurors want reassurance. They want to know that the evidence presented reflects the evidence collected. Integrity remains the foundation of persuasive expert witness testimony.
The Role of Preparation in Delivering Powerful Expert Witness Testimony
Preparation shapes the strength of expert witness testimony long before the expert enters the courtroom. Thorough preparation allows forensic professionals to refine explanations, anticipate challenges, and eliminate unnecessary complexity. Experts should review every report, revisit every forensic image, and confirm every conclusion. This disciplined review strengthens confidence and sharpens delivery.
A seasoned computer forensics expert witness also prepares for opposing arguments. They study alternative interpretations, identify potential weaknesses, and craft clear responses grounded in data. This proactive approach prevents hesitation under pressure.
Strong preparation also enhances expert testimony flow. Experts should practice transitions between methodology and findings to maintain coherence. They should refine visual aids and rehearse explanations in plain language.
When professionals working in court certified forensics invest time in structured preparation, they elevate clarity, reinforce credibility, and ensure the court fully understands the technical evidence presented.
Preparation also includes collaboration with legal counsel. Experts should clarify the scope of questioning, review courtroom procedures, and align on presentation order. This coordination prevents confusion during direct examination and strengthens the overall structure of expert witness testimony.
Experts should also conduct mock cross-examinations to test clarity under pressure. Practicing concise answers helps eliminate rambling and reinforces authority. By dedicating time to rehearsal, refinement, and strategic review, forensic professionals transform technical knowledge into persuasive, courtroom-ready communication.

Partner With Eclipse Forensics for Trusted Expert Witness Testimony
At Eclipse Forensics, we deliver precise, courtroom-ready expert witness testimony backed by decades of experience and rigorous court certified forensics standards. Our team includes seasoned specialists and a highly experienced computer forensics expert witness who understands how to translate complex digital findings into clear, compelling expert testimony.
We combine deep technical knowledge with disciplined presentation skills. We prepare every case with care. We protect evidence integrity. We communicate findings with clarity that courts respect.
If you need reliable forensic analysis and powerful courtroom presentation, contact Eclipse Forensics today. Let us help you present technical evidence with confidence and authority.