Digital forensics has changed how the authorities solve crimes. Its demand is increasing rapidly, and the industry is expected to grow at a CAGR of 10.97% by 2027. While it may offer many opportunities to solve and prevent crimes, digital data is vulnerable to cyber threats. Besides threats, analysts and investigators may also unintentionally tamper with (or alter) the evidence, making it inadmissible in court.
Category Archives: Blog
Ways to Use Digital Forensics for Cyber Crime Prevention
Cybercrime attacks are becoming a norm, as evident from the 323,972 attacks in 2021. Almost every other person on the internet fell for a cyberattack. The hack makes individuals vulnerable to losing personal data, financial information, and whatnot. If you have been a victim of cybercrime, then you must know the dangers it entails.
A digital forensic expert can help you identify the source of the attack and how to prevent it. We’re a court-certified digital forensic consultant in FL. Feel free to call us if you need an expert for your case.
Here’s how digital forensics is a great tool for preventing future cyber-attacks.
Benefits of Computer Forensics
Every computer holds a plethora of information in it. From browser history to files on your PC, everything contains pieces of evidence that may help in an investigation. Computers have been used for evidence for years, and credit goes to the forensics team for retrieving and evaluating the necessary information.
For instance, a digital forensic expert’s help is necessary in a hacking case. The hackers use all protocols to hide their identity to steal from individuals and businesses. If you’re doing a criminal investigation of a similar case, then our cyber forensic experts can help you unravel the truth.
Here are the benefits of computer forensics.
Important Tools Used by Forensic Experts
Technology has advanced with time. Forensic expert uses cutting-edge tools to look for evidence and help investigators solve a case. The equipment is used for DNA identification, analyzing drugs, and retrieving data from destroyed evidence.
If you’re searching for a digital forensic consultant who uses top-notch equipment to look for substantial evidence, then we’re the ones for you. We’re a court-certified team of digital forensic experts with years of experience.
Here’s the list of essential tools used by forensic experts.
1. Alternative Light Photography
Alternative light photography is a great tool for detecting damage to the body before it appears on the surface. Blue light and orange filters are used to detect bruises on the skin. The ultraviolet light enhances the appearance of bite marks, bruises, and other spots. Lastly, infrared photography enhances the blood that appears on the body that’s hardly visible in the dark.
2. Facial Reconstruction
Facial reconstruction is a forensic tool used to recreate an individual’s face through skeletal remains. The process is used when the person’s face is unidentified. The tool combines anatomy, artistry, osteology, and anthropology for facial reconstruction. It’s a great method to identify dead bodies or victims.
3. Drug Testing
Drug testing is quite necessary for identifying unknown substances. Presumptive tests, gas chromatography, spectrometry, etc., are some famous tests for identifying different substances. Some additional high-end tests include microcrystalline testing and ultraviolet spectrophotometry.
4. Immunochromatography
Immunochromatography is a method for identifying diseases by putting a small sample on a prepared test strip. It’s great for pregnancy tests, COVID, and HIV. Forensic expert uses this method to identify different fluids in a body.
Elevating Digital Forensic Services: Our Commitment to Excellence
In your quest for a top-tier digital forensic expert, our team stands out as a beacon of expertise, consistently delivering results through the application of high-end laboratory equipment. With certification and extensive training, our forensic computer analysts have played pivotal roles in assisting government agencies in unraveling complex cases. Our commitment to the community is evident in our ability to expedite investigations, pinpoint culprits, and exonerate the innocent.
Our dedication to remaining at the forefront of forensic science has only deepened. The incorporation of artificial intelligence (AI) and machine learning into digital forensic services has significantly augmented our capabilities. Our team has wholeheartedly embraced state-of-the-art forensic software harnessing these technologies, enabling us to sift through extensive datasets, recognize patterns, and extract valuable insights that might have otherwise eluded detection.
Furthermore, our collaboration with leading forensic research institutions has broadened our horizons. We’ve gained access to emerging technologies, such as advanced DNA sequencing techniques, bolstering our ability as data forensic experts to extract crucial information even from minute samples. The evolution of forensic tools remains a dynamic process, and our team is unwaveringly dedicated to staying abreast of these advancements to ensure we provide the highest caliber of digital forensic services.
 Embracing the Future of Digital Forensics
Embracing the Future of Digital Forensics
As the field of forensic science propels forward, our arsenal of tools becomes increasingly sophisticated. From alternative light photography to AI-driven data analysis, the forensic landscape is evolving rapidly. Our commitment to excellence, coupled with an unceasing pursuit of knowledge and technology, positions us as your premier choice for a digital forensic consultant. If you are in search of a partner in unraveling the complexities of modern investigations, contact us today – we are prepared to bring our digital forensic expertise to your team and contribute to the pursuit of justice.
Are You Searching for a Digital Forensic Expert? Call Us
When it comes to using high-end lab equipment, our team never disappoints.
We’re a court-certified lab forensic team with plenty of experience on our plate. We have helped government agencies in getting to the bottom of a case by tracing evidence. Our work has helped agencies speed up their investigation process. We’ve helped them identify culprits and prove victims innocent.
We take pride in the work we do for the community. Being digital forensic engineer, we are all certified and trained to utilize top-notch methods for discovery. If you need a digital forensic consultant on your team, call us now for help!
Is It Possible to Use Text Messages as Legal Evidence?
Text messages are a dialogue between two individuals and can be used as evidence in court. However, it’s necessary to properly verify text messages before submitting them toa court of law. It’s a good piece of evidence, but it’s still not enough to prove the victim’s innocence or the alleged person’s crime.
If you want to confirm the authenticity of the text message or need mobile forensics to recover text messages, then we can help you with it. Our digital forensic experts can analyze all necessary information for you, so get in touch today!
Main Categories of Mobile Forensics: A Guide to Extracting Data
Data recovery from mobile phones is a tricky business! That’s because many mobile phones now encrypt data. Data encryption scrambles data to the extent that only authorized persons can access it. Encrypted data is usually known as cipher text. Mobile forensics specializes in collecting and authenticating encrypting data.
Some categories of mobile forensics include:
The Basic Steps of a Crime Scene Investigation
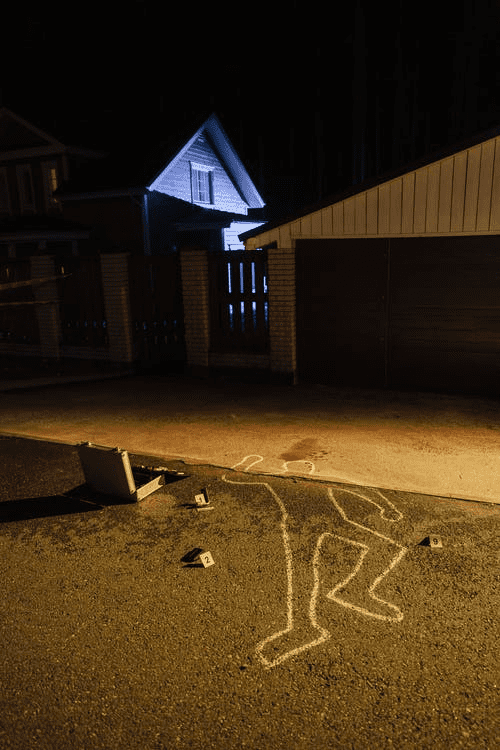
Crime scene investigation is intense. The way a case is handled changes with each new piece of evidence. However, some steps in a crime scene investigation remain similar.
Assessing Crime Dimensions
The assessment of the crime scene sets the pace for the level of examination to be conducted and the type of incident to be investigated. The prime investigator shares preliminary information and implements investigative plans according to all applicable laws. The crime scene investigation determines the plan for collecting and preserving evidence.
The Main Branches of Digital Forensics and Their Applications
With a greater dependence on cloud computing and computer systems, digital forensics now has a strong footprint in the law enforcement avenue. Credit card fraud, cases of child pornography, and audit frauds need ace digital forensic experts to assess and analyze data for court proceedings. Only in 2021, cybercrime incidents were some of the most frequently reported criminal offenses. Crimes like phishing, personal data breach, extortion, and identity theft were reported by the thousands.
To understand the extent to which digital forensics can help you with data analysis and extraction, here’s a closer look at its branches:
Computer Forensics
Previously, the words ‘computer forensics’ and ‘digital forensics’ were used interchangeably. Computer forensics extract, analyze and preserve data for criminal and court proceedings. The branch uses strategies similar to those of data recovery. They also follow some legal guidelines for data extraction.
Network Forensics
This branch of digital forensics focuses on monitoring and assessing computer network traffic for legal evidence, information gathering, or third-party intrusion detection. David Schiffer, a correspondent for Forbes, is quite certain cybercrime issues are bound to exacerbate as organizations grow their networks.
Mobile Device Forensics
The branch covers the recovery of digital evidence from phones using forensic data analysis methods. The term ‘mobile devices’ goes for all devices with GPS, internal memory, and communicative facilities. Some things that mobile forensics are still trying to decode include:
- Locating the cell phone while the mobile is on hibernation mode or is switched off
- Shifts in mobile phone form like changes in the operating system, memory storage, and peripherals like pin connectors
Recovering data from phones can get quite complex. At Eclipse Forensics, our data forensic experts can collect call logs, text messages, deleted pictures, call lists, and more data sets.
Database Forensics
Database forensics is related to metadata. The information can exist in a server’s RAM. During such a case, cyber forensic experts perform a live analysis of RAMs to extract data. A forensic examination of data includes who accessed the database and if data in the system has been tampered with. Organizations across the world have data stored in complex databases that can be analyzed to collect forensic data.
Database forensics can also identify transactions within an application database. Evidence of fraud and wrongdoing may be collected this way.
Contact Eclipse Forensics for Certified Digital Forensic Services
We are pros at uncovering electronic data for courtrooms! To avail our audio forensic and video forensic services, contact us at 9047971866.
Is Murder Different From Homicide?
Being an eye-witness to murder or even being charged with homicide can be traumatizing. According to a recent report, the murder and homicide rate in the United States was 6.52 percent in 2020. Also, per the CCJ report, homicide rates fell by 2% in the first half of 2022.
Ever wondered how many kinds of murders are there after watching “Child’s play”? Is there a difference between these killings? Most people often get confused between homicide, murder, and manslaughter.
They read the headlines or watch slasher movies and wonder why one murder convict gets a jail term while another gets incarceration for manslaughter. When people encounter terminology like “felony murder,” it becomes more perplexing. In the end, aren’t they all violent crimes?
It’s a prevalent misconception that murder and homicide are synonymous things. These two offenses differ from one another in terms of the law. Each one has a harsh punishment.
The aspects of homicide and murder necessitate a more thorough examination of both criminal codes. For that matter, Eclipse Forensics has compiled a guide to help you understand the difference between a homicide and murder.
Take a look at this guide to understand the main distinction between the two terms.
What Is Homicide?
We frequently associate murder and manslaughter with the phrase “homicide.” These are only two kinds of homicides. Homicide includes all types of murder, including those committed intentionally, negligently, or recklessly. It also includes legal killings such as those committed in self-defense, manslaughter, murder, and state-sanctioned killings.
What Is Murder?
Murder is a category of homicide in which a person kills another person. The following are the common types of murders:
1. First-Degree Murder
It is defined as a planned murder. For example, O.J. Simpson was accused of 2 first-degree murders, one of his ex-wife and another of an un-related citizen. The prosecutor filed the charges based on evidence found at the murder site, such as a bloody glove and information that Simpson may have monitored his spouse before the murders.
2. Second-Degree Murder
It is any murder committed without any premeditated motive. A famous example of a second-degree case is the George Zimmerman lawsuit. George shot Trayvon Martin African-American high school student, without any premeditated motive back in 2012.
3. Felony Murder
Let’s imagine that Bonnie and Clyde commit a bank robbery. Clyde shots the security personnel during a fight. Later he is charged with first-degree murder. Bonnie was accused of committing felony murder as she actively participated in the felony crime when the worker died.
How Can A Forensic Expert Help You?
You need to be aware of your choices and how to act if you’ve been accused of a criminal offense or if you intend to sue someone. Working with knowledgeable digital forensics professionals will help you reach a fruitful and satisfying solution for your case.
Expert digital forensic engineers are equipped with the necessary tools to examine digital evidence without turning on a computer. As a result, firms must always use professionals to collect and restore data.
Hire A Professional Forensic Expert In Florida
If you’re looking for qualified and trustworthy digital forensics specialists, get in touch with Eclipse Forensics in Florida. Our team has substantial knowledge and experience in collecting, assessing, and providing digital evidence in judicial cases. Call us right away for additional information about our digital forensic solutions.
Essential Steps Of Crime Scene Evaluation
The CCJ evaluated the crime rate of twenty-nine cities. The report was released this Thursday. The report states homicide rates fell by 2% in the first half of 2022. However, this decrease is unsatisfactory. The report also stated about other crimes with their increased rates like robbery (19%), property theft (6%), and car theft (15%).
This hike has alarmed corporate companies and law enforcement departments. These sectors are now working on creating the best forensic teams to help them solve any crimes, whether IP theft or a murder case.
Have you ever wondered how a crime scene is evaluated? Take a look at this guide to learn about some essential steps of crime scene evaluation.
1. Examine The Crime Site
the law enforcement officers and detectives rush to the site when a crime is reported. The first step is to examine the crime scene. The team studies the site, nearby locations, the site’s utensils, blood samples, food samples, body (if any), phone data, computer data, CCTV footage, and collects other forensic evidence. This practice helps them to find clues to solve the crime.
2. Take Photographs
It’s best to take pictures after collecting all the required samples. This practice helps law enforcement officers to assess the crime scene more carefully. Also, if a criminal destroys any evidence, these pictures will help the officers identify what was stolen or destroyed.
3. Seal The Crime Site
The police seal the crime scene after examining the site and collecting all the evidence. This step helps them to keep the suspects and criminals away from the site. In some cases, the criminal returns to the site to destroy the evidence or retrieve their belonging left at the crime scene.
4. Speaking To Eyewitnesses/Nearby People
The next step is to speak to eyewitnesses or people living nearby the crime site. This practice helps the investigators to find the suspects and have a clear perspective about the victim’s life and intrapersonal relations with family and friends.
5. Conducting A Secondary Survey
The investigators and forensics team conduct a secondary survey to ensure no clues are left behind, and all the pieces are connected to find the criminal.
6. Catch The Criminal
After completing all pieces of the puzzle, you will have a prime suspect/criminal. The final step is to arrest the criminal and present it to the court.
Why Your Company/Department Needs Cyber Forensic Experts
The term “intellectual property theft” describes situations in which a person steals a product or an idea from a business or another person. Theft of a company’s private information, brand names, copyrights, and designs are all examples of IP theft.
However, recognizing IP theft can be intimidating in a world where a few clicks can jeopardize a firm’s private data. This is where digital forensic experts come into the picture. Experts in digital forensics are essential for successfully managing cases of potential intellectual property theft.

Get In Touch With One Of The Most Reliable And Trustworthy Cyber Forensic Service Provider In Florida
Are you looking for a professional cyber forensic expert in Florida? Eclipse Forensicsis here to help you. We aim to help other companies and departments to shield their companies against cybercrimes. We have worked on numerous cases since 2005 for governmental agencies, independent lawyers, and citizens.
We provide affordable audio forensics, video forensics, and data forensics services. Contact us now for more details about our premium services.