In today’s digital landscape, mobile devices are more than just communication tools—they are repositories of personal, financial, and operational data. From text messages and call logs to app activity and geolocation history, smartphones hold a wealth of information that can become crucial in investigations, litigation, and corporate inquiries. As technology evolves, so do the methods required to retrieve and analyze this data.
Mobile device forensics has emerged as a specialized field focused on uncovering hidden or deleted information from smartphones and tablets in a legally sound manner. This blog explores advanced techniques used by experts to recover critical data, offering valuable insight into how modern forensic processes work.
The Foundations of Mobile Investigations
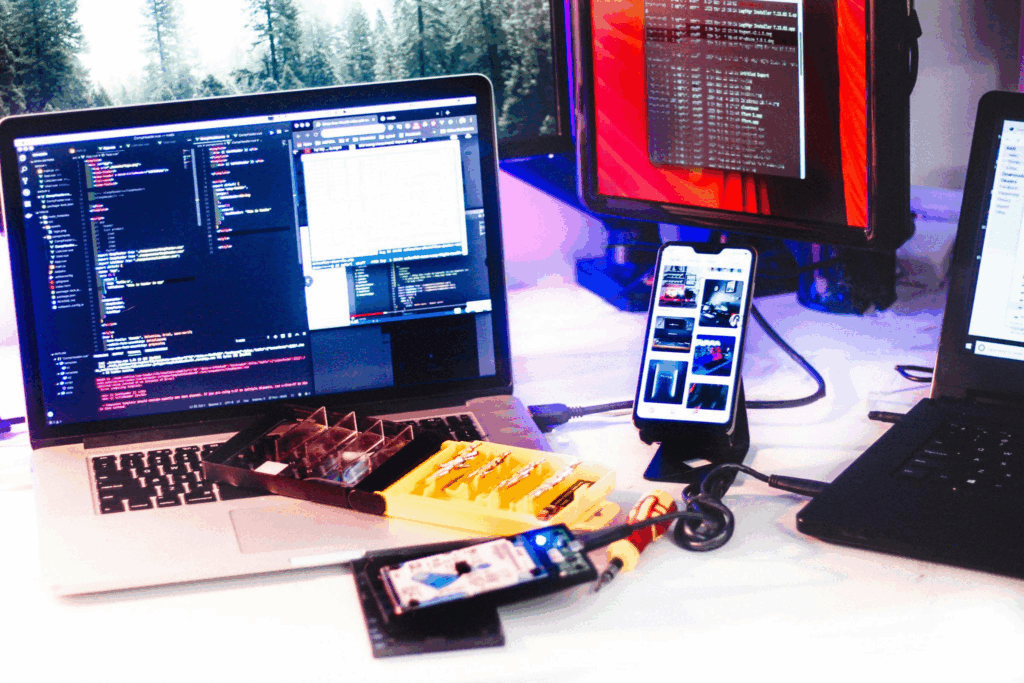
At its core, mobile device forensics involves the identification, preservation, extraction, and analysis of data from mobile devices. Unlike traditional computers, mobile devices operate on diverse operating systems such as Android and iOS, each with unique file structures and security protocols.
Forensic experts begin by securing the device to prevent data alteration. This often involves isolating it from networks using airplane mode or specialized shielding techniques. Once preserved, experts create a forensic image—a bit-by-bit copy of the device’s storage—ensuring that the original data remains untouched throughout the investigation.
This foundational process sets the stage for deeper analysis, allowing investigators to explore user activity, app data, and hidden files with accuracy and integrity.
Extraction Methods in Mobile Analysis
A key component of investigations involves cell phone forensic services, particularly when selecting the right extraction technique. Logical extraction retrieves accessible data such as contacts, messages, and media files through standard system interfaces. It is less invasive and often quicker but may not recover deleted or hidden information.
Physical extraction, on the other hand, involves accessing the device’s raw memory. This method enables forensic experts to recover deleted files, fragments of data, and system-level artifacts that are not visible through conventional means. Advanced tools and techniques are required, especially when dealing with encrypted or locked devices.
Choosing the right extraction method depends on the case requirements, device condition, and legal considerations.
Recovering Deleted and Hidden Data
Recovering lost information often requires the expertise of a data forensic expert who understands how data behaves beneath the surface. Techniques such as file carving, memory analysis, and database reconstruction are commonly used to uncover fragments of deleted files.
File carving allows experts to recover data by scanning raw storage for recognizable patterns, while memory analysis can reveal temporary data such as passwords or recent activity. Database reconstruction helps piece together app-based records that may appear incomplete after deletion.
These advanced approaches allow investigators to rebuild digital timelines and uncover critical insights that would otherwise remain hidden.
Overcoming Security and Encryption Barriers
Modern smartphones are designed with robust security features, making them challenging to access during investigations. A cyber forensic expert applies specialized strategies to navigate these protections without compromising data integrity.
This may include leveraging authorized access methods, analyzing system vulnerabilities, or retrieving information from synchronized backups. Encryption is intended to safeguard user data, but with the right expertise and legal authorization, valuable information can still be accessed.
These techniques ensure that investigations remain thorough while respecting privacy and compliance standards, maintaining data integrity, minimizing risks, and providing legally defensible results for all stakeholders involved.
Multimedia Evidence and Its Importance
Mobile devices often store a significant amount of multimedia data, which can serve as crucial evidence. Through digital video forensics, experts examine videos for authenticity, detect manipulation, and enhance visual clarity.
This process involves analyzing metadata, frame structures, and compression patterns to determine whether a file has been altered. Enhancement tools can improve visibility in low-quality footage, making it easier to identify important details.
Multimedia analysis plays a vital role in cases where visual or audio evidence is central to understanding events, helping verify authenticity, detect tampering, and provide clear, actionable insights for investigators.
Connecting Data across Multiple Platforms
A comprehensive investigation often requires linking mobile data with other digital sources. A computer forensic analyst examines how information flows between devices such as laptops, tablets, and cloud systems.
For example, a message sent from a smartphone may also appear on a synchronized computer, while backups stored in the cloud can provide additional context. By correlating data across platforms, investigators can verify timelines and identify discrepancies.
This cross-device approach strengthens the overall reliability of forensic findings and provides a broader understanding of user activity.
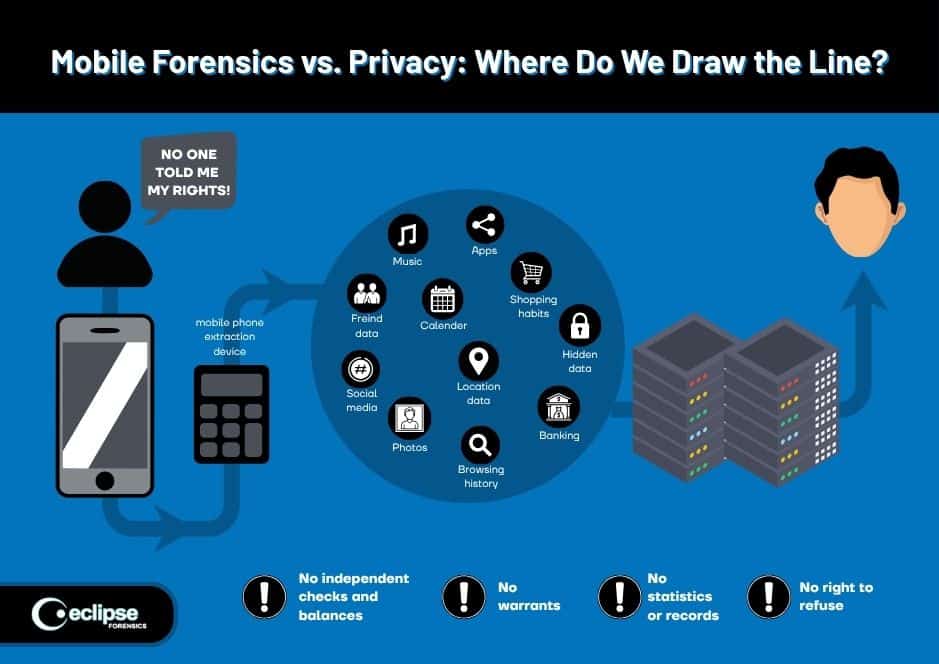
Expanding Investigations beyond the Device
Today’s mobile devices are deeply integrated with cloud services and applications. Utilizing digital forensic services, investigators can access data stored beyond the physical device, including cloud backups and app-based records.
This process involves analyzing account activity, login histories, and synchronization logs to recover additional evidence. Even if data is deleted from the device, it may still exist in remote storage.
By extending investigations into the cloud, forensic experts can reconstruct digital activity more comprehensively and accurately.
Turning Technical Findings into Clear Evidence
The final step in any investigation is presenting findings in a clear and structured manner. A digital forensic consultant plays a crucial role in translating technical data into understandable reports.
These reports outline the methods used, evidence recovered, and conclusions drawn, ensuring that stakeholders can interpret the results. In legal contexts, these findings must be precise and defensible.
Clear reporting ensures that digital evidence can effectively support decision-making, whether in courtrooms or corporate environments.

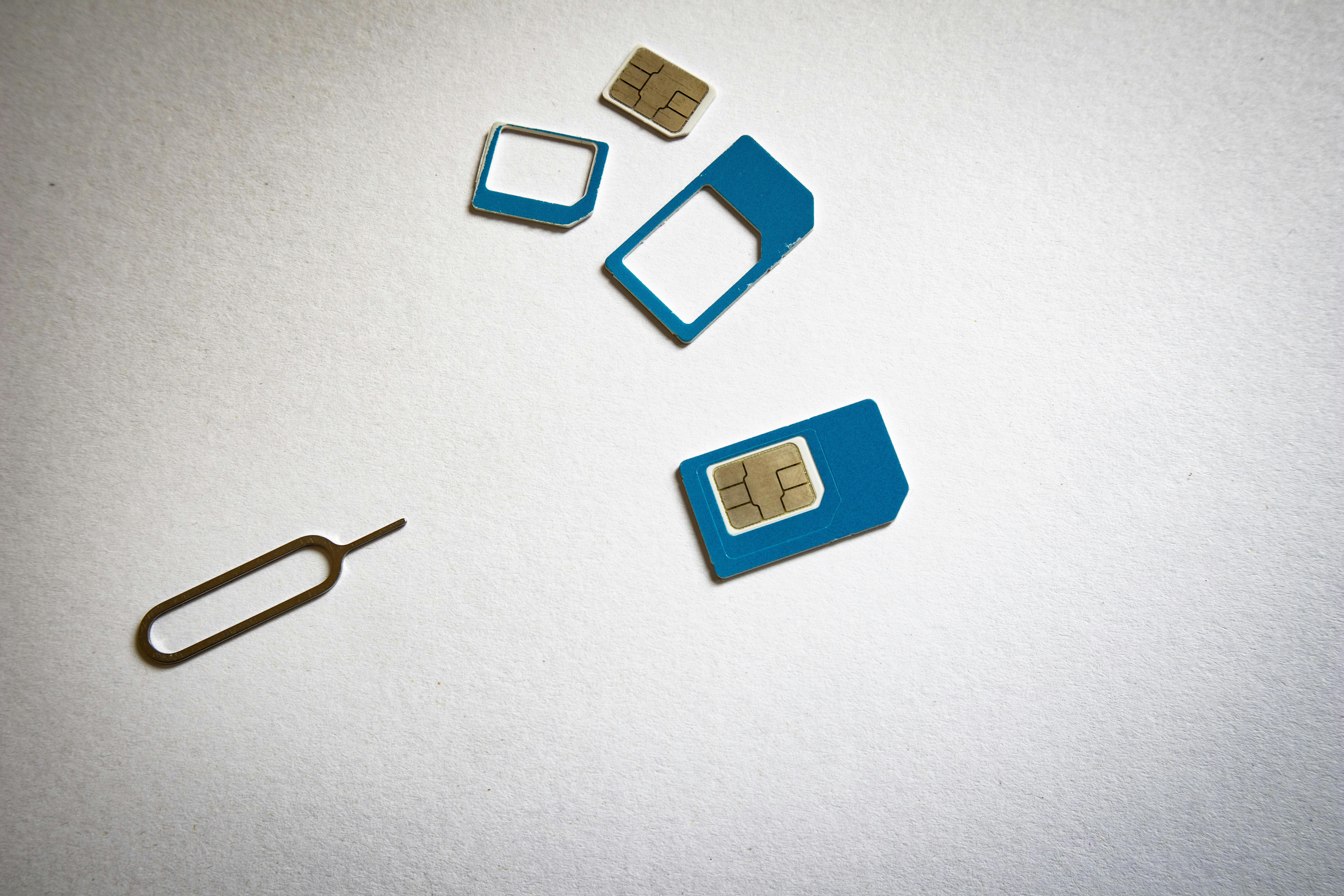
SIM Card and Network Data Analysis
Another critical layer of investigation involves examining SIM cards and network-related data through cell phone forensics standards and methodologies. SIM cards store valuable information such as contact lists, SMS data, and network identifiers that can help establish communication patterns.
In addition to SIM data, forensic experts analyze network logs, carrier records, and connection histories to track device activity over time. This type of analysis can reveal location patterns, call behaviour, and even interactions between multiple devices. By combining SIM and network data, investigators gain a clearer understanding of how a device was used within a broader communication ecosystem.
Beyond these elements, specialists may also examine International Mobile Subscriber Identity (IMSI) numbers, SIM application data, and authentication keys, which help verify the identity of the subscriber and the network used. Analysts can correlate this information with Call Detail Records (CDRs) provided by mobile carriers to reconstruct timelines of calls, text messages, and data sessions. In many investigations, this correlation helps identify when a device connected to specific cell towers, which can assist in approximating the device’s geographic movement.
Enhancing and Authenticating Audio Evidence
Audio data can be just as important as visual or textual evidence in mobile investigations. Through specialized audio forensic services, experts can enhance recordings, reduce background noise, and clarify speech for better interpretation.
Beyond enhancement, authentication plays a key role in determining whether an audio file has been altered or manipulated. Experts analyze waveform patterns, frequency inconsistencies, and metadata to verify integrity. These techniques are especially valuable in legal and investigative contexts where the credibility of recorded conversations is essential.
Discover the Difference with Trusted Forensic Expertise
At Eclipse Forensics, we recognize how essential it is to uncover reliable digital evidence in complex situations. Whether you are navigating a legal dispute or conducting an internal investigation, having accurate insights can make all the difference. Through advanced mobile device forensics, we help reveal critical data that supports informed decisions and strengthens your case.
What makes our approach unique is the depth of expertise we bring to every investigation. From detailed data recovery to comprehensive analysis, our team ensures that every step is handled with precision and professionalism. By combining technical excellence with proven computer forensic analyst techniques, we deliver results you can rely on.
To learn more about our approach and the expertise behind Eclipse Forensics, we invite you to explore further. To discuss your specific needs and explore how we can help, reach out to our team today and take the next step toward uncovering the digital truth with confidence through our digital forensic services.