In today’s digital age, our lives are increasingly intertwined with technology. We document our experiences, conduct business, and communicate with loved ones – all through a constant stream of emails, texts, social media posts, and digital files. But what happens when this digital footprint becomes crucial evidence in a legal case?
The Power of the Invisible: Unveiling the Voice of Digital Evidence
A staggering 90% of all criminal cases now involve some form of digital evidence. From deleted text messages to hidden browser history, these digital traces can hold the key to uncovering the truth.
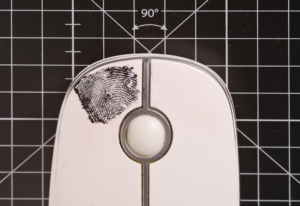
However, unlike a physical fingerprint or a witness testimony, digital evidence is often invisible to the naked eye. It requires specialized expertise to collect, analyze, and present it in a way that is admissible in court.
This is where digital forensic engineers and consultants come in. They act as the voice for this silent witness, meticulously sifting through the digital landscape to recover, analyze, and interpret potentially crucial evidence.
The Digital Forensics Process: Unmasking the Truth
The digital forensics process is a meticulous and crucial step in any legal case that involves digital evidence. Here’s a breakdown of the key steps:
1. Collection: The Art of Secure Acquisition
Imagine a crime scene, but instead of fingerprints and footprints, we’re dealing with digital footprints. The first step involves collecting the potential evidence – computers, mobile devices, and storage media (like hard drives and USB sticks). This can happen in various ways, depending on the situation.
- Law enforcement seizures:In criminal investigations, law enforcement officers may seize devices with warrants. This process is strictly documented to ensure an unbroken chain of custody – a chronological record of everyone who has handled the evidence, preventing any questions about its authenticity in court.
- Civil litigation:In civil cases, the collection process might involve requesting the opposing party to surrender their devices for examination. Legal protocols are followed to ensure both parties are aware of their rights and that the process is conducted fairly.
- Internal investigations:Companies facing internal issues may need to collect employee devices to investigate potential misconduct. This requires clear internal policies and employee consent when possible.
- No matter the scenario, security is paramount.Digital forensic engineers use specialized tools to create write-protected forensic copies of the devices. This ensures the original evidence remains untouched while the copy is used for analysis. Think of it like photocopying a document for investigation while keeping the original safe.
2. Preservation: Safeguarding the Digital Voice
Once collected, the digital evidence needs to be treated with kid gloves. Any alteration or modification could render it useless in court. Here’s how we ensure its pristine condition:
- Write-blocking:The forensic copies are stored on write-blocked media, preventing accidental or intentional changes.
- Secure storage:The copies are kept in a secure and controlled environment, with access restricted to authorized personnel.
- Documentation:Detailed records are maintained, documenting the chain of custody, storage location, and any actions taken on the evidence.
3. Analysis: Unveiling Hidden Secrets

Now comes the detective work! Digital forensic engineers utilize a variety of sophisticated tools and techniques to unearth hidden information:
- Data carving:This technique recovers fragments of deleted files, like pieces of a shattered puzzle, that can be reassembled to reveal lost information.
- Metadata extraction:Every digital file carries metadata – hidden information like creation dates, last accessed times, and even previous versions. This data can provide valuable insights into user activity.
- Internet activity analysis:Examining browser history, downloaded files, and online communications can reveal a user’s online footprint and potential connections to relevant activities.
- Mobile device forensics:Mobile devices present a unique challenge, with a vast amount of data stored in various locations. Specialized tools are used to extract call logs, text messages, app data, and even location information.
By partnering with Eclipse Forensics, you gain access to a comprehensive suite of digital forensics services designed to meet your specific needs. We are committed to providing our clients with the highest quality service and support, ensuring that digital evidence is effectively utilized to achieve a successful outcome.
Don’t let the voice of your digital evidence go unheard. Contact Eclipse Forensics today, and let us help you speak volumes in court.
4. Interpretation: Making Sense of the Digital Story
The raw data extracted during analysis is just the beginning. Digital forensic consultants then interpret this data in the context of the specific case. This might involve:
- Identifying timestamps:Timestamps on files and activities can establish timelines and potential alibis or contradictions.
- Analyzing user activity:Patterns of user activity can reveal hidden connections or suspicious behaviors.
- Identifying inconsistencies:Inconsistencies between different forms of evidence, like discrepancies in timestamps or deleted files, can raise red flags and require further investigation.
5. Reporting: Presenting a Compelling Narrative
The final step involves creating a comprehensive report that translates the technical findings into a clear and concise narrative for legal teams and the court. This report should include:
- A detailed description of the collection and analysis process.
- A summary of the extracted data and its relevance to the case.
- Clear and concise explanations of technical terms ensure the report is understood by non-technical audiences.
- Visual aids like charts and timelines to effectively showcase the findings.
This report becomes a powerful tool for legal professionals, laying the groundwork for presenting digital evidence in a way that strengthens their case.
The Art of the Digital Forensic Consultant: Building a Case on Solid Ground
Beyond technical expertise, a skilled digital forensic consultant also possesses a deep understanding of legal procedures and the rules of evidence. They can effectively communicate complex technical concepts to a judge and jury, ensuring the digital evidence is presented in a way that is both compelling and admissible.
Their role goes beyond simply presenting the data. They can also help identify potential weaknesses in the opposing side’s digital evidence, further strengthening your case.
The Different Voices of Digital Evidence: Unveiling a Spectrum of Information

Digital evidence comes in many forms, each with its own unique voice:
- Computer Forensics: This involves examining digital devices like computers, laptops, and tablets. The recovered data can include emails, documents, browsing history, and deleted files.
- Mobile Device Forensics: With the ever-increasing importance of smartphones and tablets, mobile device forensics plays a crucial role. This can involve extracting call logs, text messages, location data, and app activity.
- Digital Video Forensics: Video evidence can be incredibly powerful in court, but it can also be manipulated. Digital video forensics ensures authenticity, analyzes video content for hidden details, and can even recover deleted footage.
- Data Recovery: Sometimes, crucial evidence may be accidentally deleted or hidden. Data recovery techniques can help retrieve this seemingly lost information.
The Importance of Working with a Reputable Digital Forensics Company
The stakes in legal cases involving digital evidence are high. Working with a reputable and experienced digital forensics company like Eclipse Forensics provides several key advantages:
- Expertise:Our team of certified professionals possesses the in-depth knowledge and experience needed to handle all aspects of digital forensics investigations. We stay up-to-date with the latest tools and techniques to ensure the most comprehensive analysis possible.
- Preservation and Chain of Custody:We maintain the strictest protocols to ensure the integrity of the evidence throughout the entire process. This is crucial for ensuring its admissibility in court.
- Communication and Reporting:We understand the importance of clear and concise communication. Our reports are easy to understand for both legal teams and the court, effectively presenting the digital evidence in a way that strengthens your case.
- Experience in the Courtroom:Our team has extensive experience working with legal professionals and presenting digital evidence in court. We can guide you through the process and ensure your case is presented effectively.
Let the Silent Witness Speak for You
Digital evidence is a powerful tool in the courtroom, but it requires a skilled translator to unlock its voice. By working with a reputable digital forensics company like Eclipse Forensics, you can ensure that this silent witness speaks volumes for your case.
Contact Eclipse Forensics Today
Don’t underestimate the power of digital evidence. If you are facing a legal case that may involve digital evidence, don’t hesitate to contact Eclipse Forensics. Our team of experienced digital forensic consultants is here to help you navigate the complexities of digital forensics and ensure that every piece of relevant evidence is identified, collected, analyzed, and presented in a way that strengthens your position.
Let Eclipse Forensics be your trusted partner in the world of digital forensics. We are confident that our expertise and experience can make a significant difference in the outcome of your case. Contact us today to schedule a consultation and learn how we can help you speak volumes with your digital evidence.