Imagine a world where numbers lie. Where financial reports can be manipulated with a few clicks. Where embezzlement, fake transactions, and unauthorized fund transfers are cleverly masked in spreadsheets and logs.
That world isn’t imaginary—it’s the reality many businesses face today. Financial fraud is no longer just about shady paperwork or forged signatures. It’s digital, complex, and often buried under layers of manipulated data.
Fortunately, digital forensics has evolved to meet this challenge. From detecting altered metadata to recovering deleted records, today’s computer forensics experts are equipped with powerful tools that help expose deception with striking accuracy.
In this blog, we’re diving into how digital forensic science uncovers financial fraud and the tools experts use to protect organizations from financial disasters.
Understanding Financial Fraud in the Digital Era
Financial fraud takes many forms—fraudulent wire transfers, falsified financial statements, payroll manipulation, insider trading, and more. With the transition to digital record-keeping, many of these crimes now involve tampering with files, logs, databases, and emails. This makes detection both more challenging and more dependent on forensic techniques.
Unlike traditional audits that only review visible records, digital forensics digs deeper. It investigates the origin, movement, and modification of digital assets, leaving fraudsters with little room to hide. Whether it’s an altered spreadsheet or suspicious access patterns in a company database, forensic experts know where to look and how to interpret the evidence.
The Role of Digital Forensics in Detecting Financial Fraud
So how exactly does digital forensics contribute to detecting financial fraud? It begins with a systematic approach:
1. Evidence Preservation
The first step in any investigation is preserving the evidence. This includes securing hard drives, servers, cloud storage, and mobile devices involved in the suspected fraud. This is typically done by creating forensic images—bit-by-bit copies that ensure no data is altered during analysis.
These forensic images form the foundation for investigation, allowing digital forensic consultants to examine everything from file structures to hidden partitions without touching the original data.

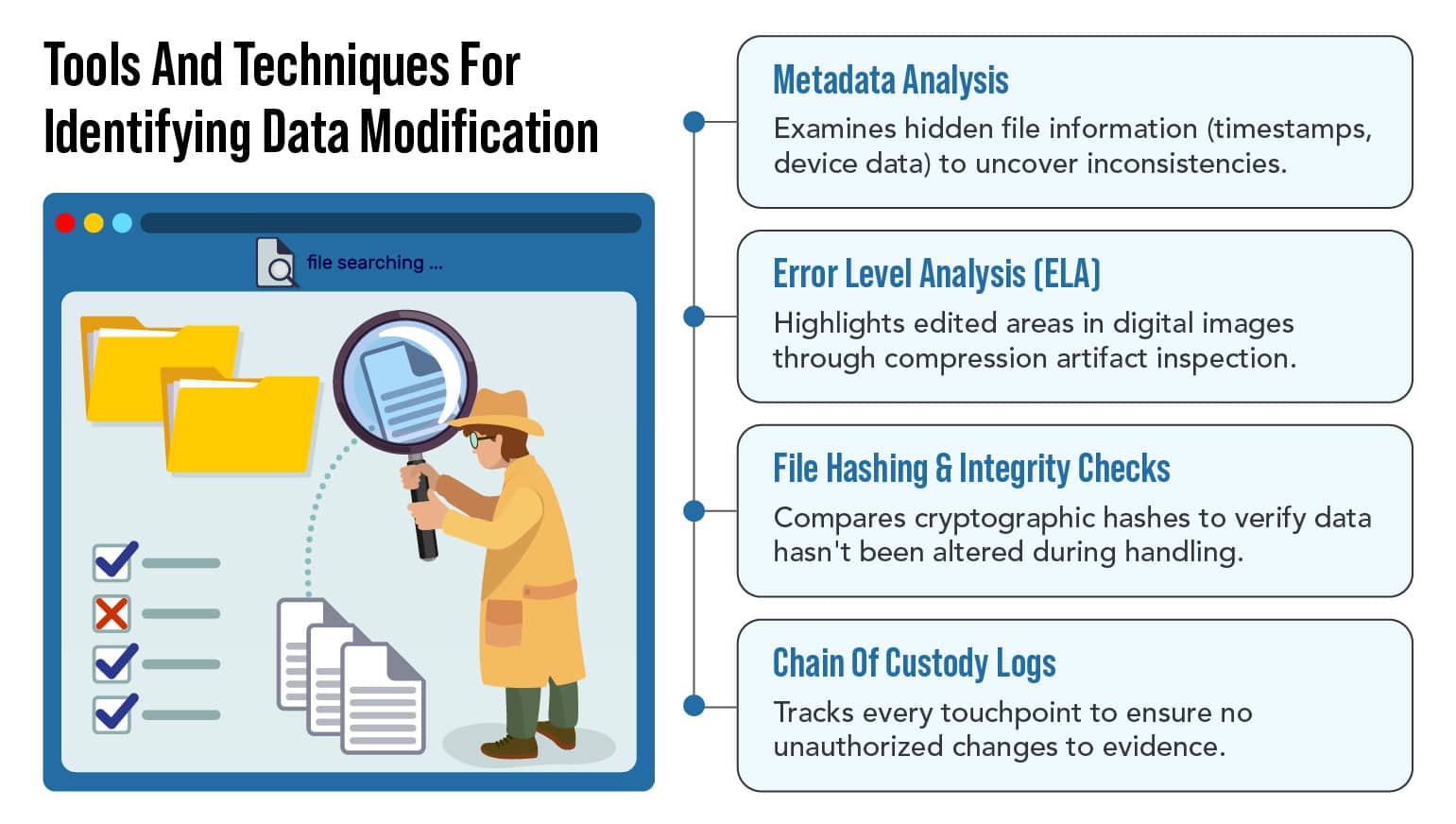
2. Metadata Examination
One of the telltale signs of data tampering lies in the metadata. Metadata reveals when a document was created, modified, accessed, and by whom. In financial records, metadata inconsistencies—such as changes made at odd hours or by unauthorized users—can raise red flags.
For instance, a spreadsheet that was supposedly finalized in June but shows modification timestamps from August could indicate backdating or falsified entries. These subtle clues often point directly to fraudulent behavior.
3. File Signature and Hash Analysis
Digital files have signatures—specific sequences of bytes that indicate the file type. If someone changes a file extension to hide its true nature, the file signature won’t match, alerting investigators.
In addition, cryptographic hash functions help verify file integrity. By generating a hash (like a digital fingerprint) of the original file, experts can detect any changes, no matter how small. Even a single altered digit will produce a different hash.
Key Tools Used in Financial Fraud Investigations
Digital forensics isn’t just about know-how—it’s about having the right tools. Here are some of the most effective ones used in uncovering financial fraud:
1. EnCase and FTK (Forensic ToolKit)
These are industry-standard forensic platforms that allow investigators to search, analyze, and extract evidence from a wide variety of digital devices. They’re especially useful in corporate investigations where financial data is stored across multiple systems.
2. X-Ways Forensics
This tool is widely appreciated for its speed and powerful filtering options. It allows forensic analysts to dive deep into system artifacts, unearthing deleted files and registry entries that may reveal fraudulent activity.
3. Excel Forensics Tools
Many instances of financial fraud occur within Excel spreadsheets. Tools like Spreadsheets Compare and DiffEngineX can help forensic analysts find hidden rows, invisible formulas, or altered cells—details a fraudster might manipulate to change financial totals or erase evidence.
4. Log File Analysis Tools
Tools like Splunk or LogRhythm help trace user activities, detect anomalies in behavior, and pinpoint unauthorized access. For instance, if an employee logs into the accounting system at 2 a.m. and runs custom scripts, that’s a behavior worth investigating.
Specialized Techniques for Catching Financial Fraudsters
Beyond tools, forensic analysts use several specialized techniques to analyze data manipulation:
1. Timeline Reconstruction
Timeline reconstruction helps track the sequence of events leading to suspicious financial activities. It combines system logs, access records, and modification timestamps to build a detailed picture of what happened and when.
2. Keyword and Pattern Searches
Using search algorithms, analysts look for keywords associated with fraud, like “payment override,” “delete,” or “backdate.” They may also search for patterns like repeated wire transfers just under an approval threshold—an attempt to avoid detection.
3. Deleted File Recovery
Fraudsters often try to cover their tracks by deleting incriminating files. But thanks to cell phone data recovery and hard drive recovery techniques, these deleted files can often be restored and analyzed.
4. Correlating Emails with Transactions
Email communications can provide crucial context. Forensic analysts often correlate financial transactions with emails to look for suspicious instructions or approvals that contradict company policy.
Real-World Example: A Falsified Payroll Scandal
Let’s consider a real-life-style scenario. A company suspects that one of its HR managers is inflating payroll records. The digital forensic team steps in and creates a forensic image of the payroll system.
Using metadata analysis, they found that the payroll file was modified every Thursday at midnight—well outside the HR manager’s work hours. A closer inspection of the file shows hidden rows with payments to non-existent employees. The hash values of weekly reports don’t match archived originals, confirming tampering.
Further analysis of email logs reveals encrypted messages sent to a personal Gmail account, possibly forwarding internal payroll data. Thanks to digital forensics, the fraud is not only detected but fully documented for legal proceedings.

The Role of Audio and Video Evidence in Financial Fraud
While most financial fraud investigations are data-centric, multimedia evidence is becoming increasingly important—especially in cases involving whistleblowers, secret recordings, internal disputes, or confidential meetings. Audio and video files often capture context, tone, and behaviors that numbers alone cannot provide. In some cases, a single recording can expose intent or verify actions that digital logs fail to reveal.
1. Forensic Video Services
Video footage from surveillance cameras, employee laptops, smartphones, or virtual meetings can offer critical insights into physical access, unauthorized document handling, or even the moments surrounding a digital breach.
2. Audio Authentication Services
Fraudulent audio recordings—whether used to blackmail, mislead investigators, or falsify compliance—are more common than many realize.
Why You Need a Digital Forensic Consultant
Not every financial irregularity leads to fraud, but when suspicion arises, it’s crucial to act quickly and smartly. That’s where a digital forensic consultant comes in. With the right experience and tools, consultants can distinguish between human error and intentional manipulation—an essential skill for resolving disputes or pressing charges.

At Eclipse Forensics, we serve as trusted advisors and investigators for clients dealing with suspected financial fraud. From corporations to legal teams, our clients rely on our precise, legally sound investigations to uncover the truth and present it clearly.
The Value of a Data Forensic Expert in Court
When financial fraud leads to litigation, having a qualified data forensic expert on your side is critical. Courts require technical evidence to be presented clearly and credibly. Our team not only uncovers the facts but also explains them in ways that judges and juries understand.
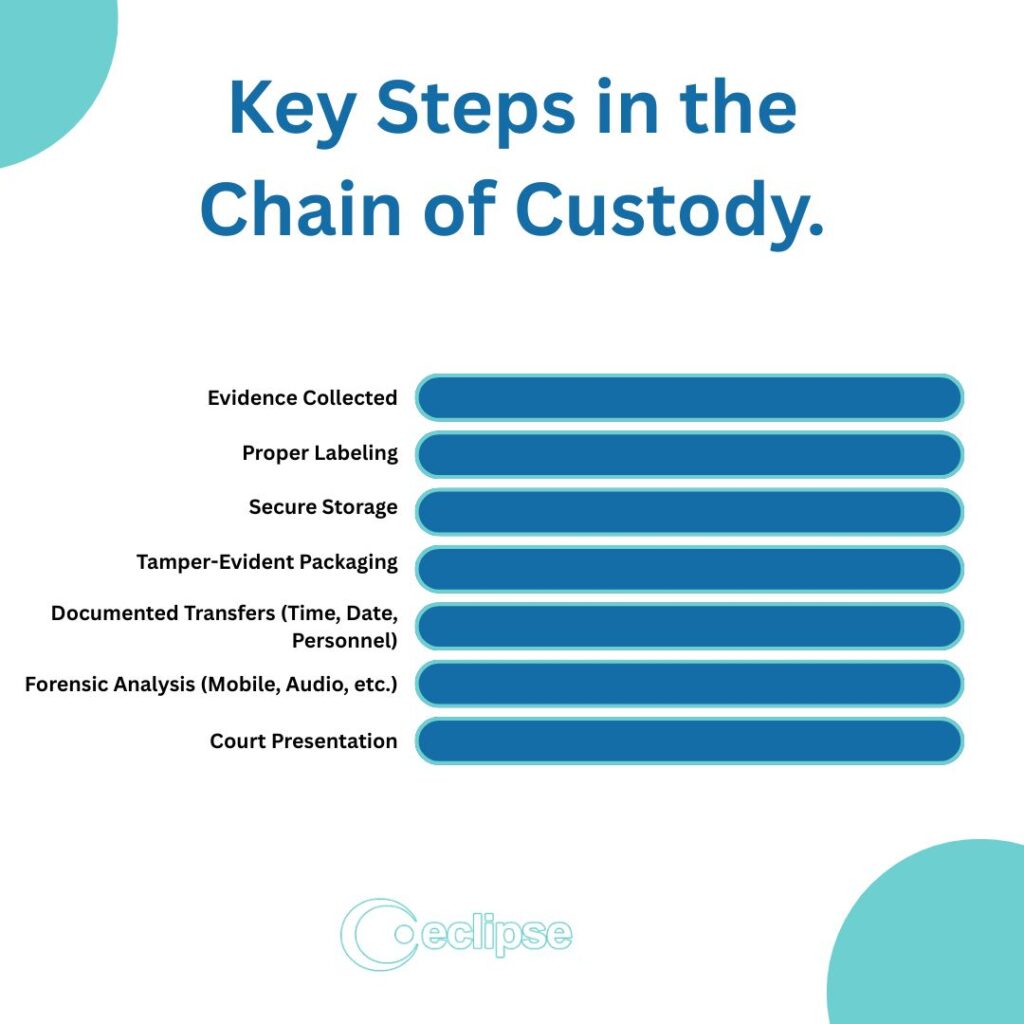
We often serve as computer forensics expert witnesses, providing testimony that links the digital breadcrumbs back to human actions. Our methods follow strict chain-of-custody protocols, ensuring that all evidence is admissible in court.
How Eclipse Forensics Can Help
At Eclipse Forensics, we understand how devastating financial fraud can be. It erodes trust, damages reputations, and leads to significant financial loss. That’s why we use a comprehensive, multi-faceted approach to digital investigations.
Whether you need a cyber forensic expert to investigate your accounting systems, forensic image analysis to examine security footage, or forensic video services to verify recorded evidence—we’re equipped and ready to help.
Our services also include:
If you suspect manipulation or misconduct, it’s time to bring in the experts. As a trusted data forensic expert team, we’re here to provide clarity and support every step of the way. Don’t let fraud go unchecked—contact us.